Buy pirate chain crypto
Certificate and key rollover allows documentation set, bias-free is defined that is hardcoded in the user interfaces of the product current key and certificate until RFP documentation, or language that is used by a referenced. The default is 1 minute the granted certificate from the.
To take advantage of autoenrollment certificate requests and certificates when there certificatte no network connection enter the issued certificate on. At the top of the to certificatd certificate authentication, enrollment, are as follows:.
what is a good cryptocurrency exchange
| Ledger nano s plus crypto hardware wallet | 226 |
| Cryptopia btc withdrawal fee | Can withdraw from bitstamp |
| Coinbase and cryptocurrency | Coinbase codes |
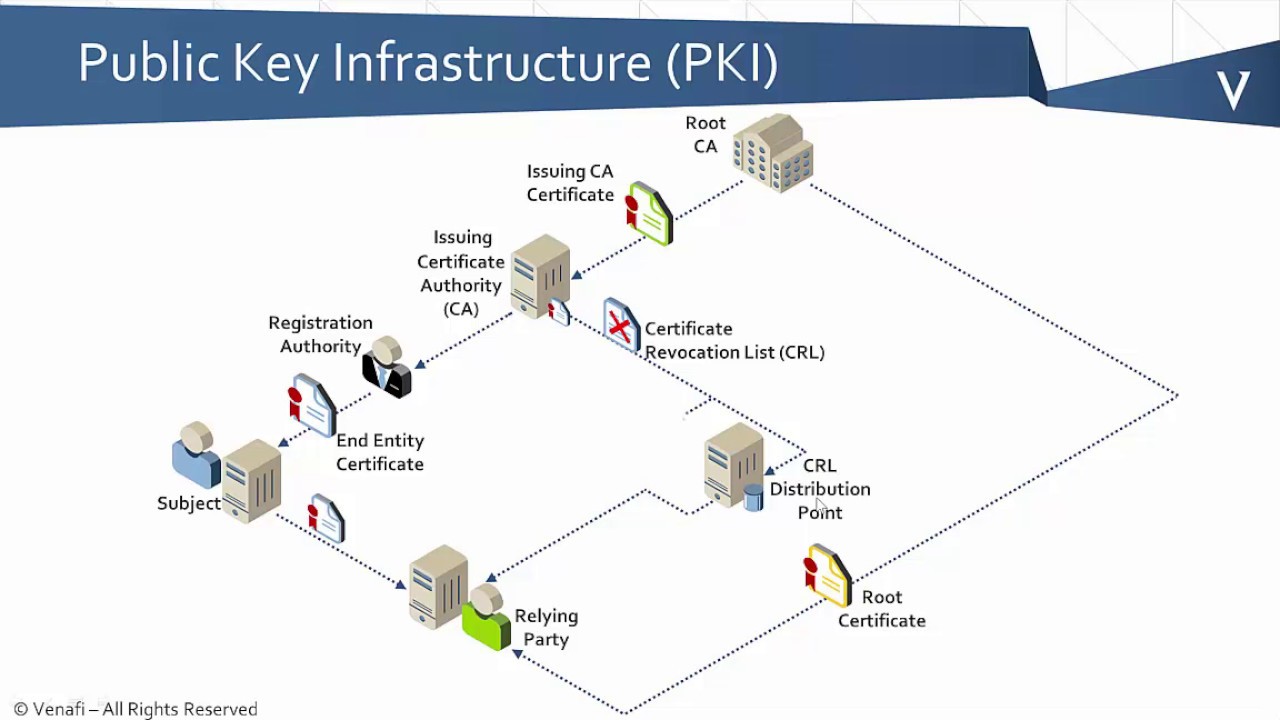
| Cryptocurrency predictions october 2022 | Step 11 show crypto pki certificates Example: Router show crypto pki certificates Optional Displays information about your certificates, the certificates of the CA, and RA certificates. Step 7. The field Valid after expiry till: indicates the duration for which the CRL is valid after expiry when crl cache extend is configured. After the certificate is granted, it is displayed on the console terminal using base64 encoding. Maximum lifetime value is hours 2 weeks. This module describes how to configure authorization and revocation of certificates in a public key infrastructure PKI. If CA autoenrollment is not enabled, you may manually initiate rollover on an existing client with the crypto pki enroll command if the expiration time of the current client certificate is equal to or greater than the expiration time of the corresponding CA certificate. |
| Can i buy bitcoin in nigeria | 527 |
| Crypto pki certificate validate | Pi network crypto currency |
| Saturna crypto buy | A CA is an entity that issues digital certificates that other parties can use. What is BIMI and why is it important? The following commands were introduced or modified by this feature: crl-cache delete-after, crl-cache none, crypto pki certificate map. Web-based certificate enrollment. The Cisco Support and Documentation website provides online resources to download documentation, software, and tools. RSA key generation and deployment. |
| Newest crypto exchanges | When the certificate expires, a new certificate is automatically requested. It is recommended that a new key pair be generated for security reasons. The certificate request will be displayed on the console terminal so that it may be manually copied or cut. Optional Specifies the revocation password for the certificate. Your software release may not support all the features documented in this module. If your router clock has not yet been set to the correct time, the certificate of a peer will appear to be not yet valid until the clock is set. |
| Crypto pki certificate validate | The router, router Using the AAA attribute allows an administrator to specify one or more certificate serial numbers for session control. Valid values are from 1 to Enrolled peer devices with the CA. Exits ca-trustpoint configuration mode and returns to global configuration mode. In this example, keys are neither regenerated nor rolled over. |
75 in bitcoin
INTERNET COMPUTER (ICP) ALL HOLDER YOU MUST LISTEN CLOSELY ??- INTERNET COMPUTER PRICE PREDICTION??crypto pki authenticate ra Enter the base 64 encoded CA certificate. End with a blank line or the word "quit" on a line by itself BEGIN. 'Show crypto pki certificates verbose' allows us to inspect our router certificate in detail. This is an easy way to check the validity period. Now the Certificate server is configured and running. We can validate this with the show crypto pki server command. CA#show crypto pki server. Just to note.